Iranian Hacking Group Targets U.S. Election Infrastructure, Microsoft Reports
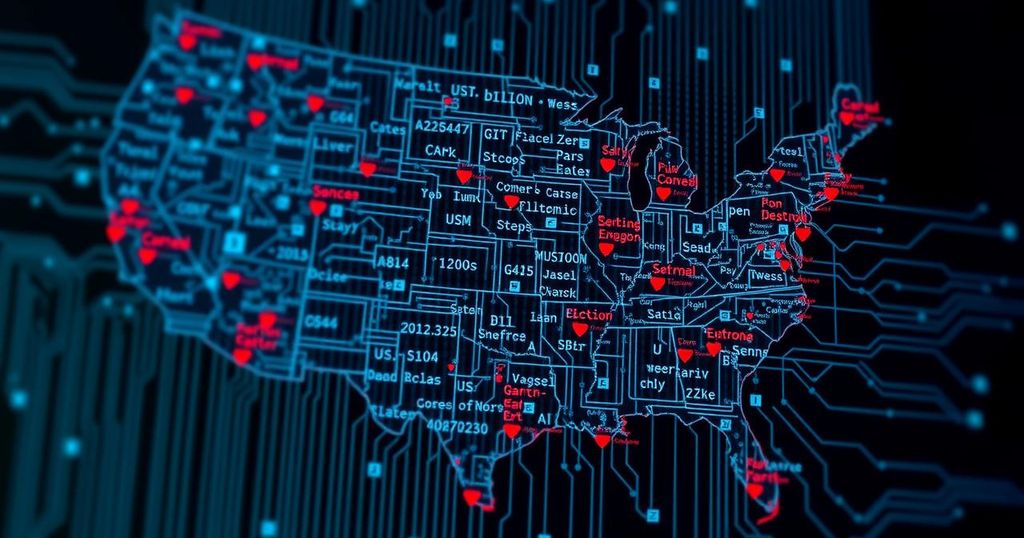
Iranian government-affiliated hackers have targeted U.S. election-related websites in swing states to identify vulnerabilities ahead of the presidential election, according to Microsoft. This activity adds to existing concerns over foreign interference and misinformation campaigns aimed at the electoral process, following a history of similar activities and preparations from other state actors.
Iranian hackers with links to the government have been identified as probing various election-related websites within key swing states in the United States, according to a report released by Microsoft. This activity appears to be an effort to identify potential vulnerabilities ahead of the presidential election. The probing took place in April, but analysts from Microsoft only recently uncovered it. Additionally, the hackers conducted reconnaissance on major U.S. media outlets in May. U.S. intelligence officials have indicated that Iran’s efforts may be aimed at sowing discord during the 2024 election cycle, coupling this with hacking activities targeting former President Donald Trump’s campaign and promoting protests related to U.S. policies on Israel. Microsoft analysts are wary that the hacking group, referred to as “Cotton Sandstorm,” which they believe is operated by Iran’s Islamic Revolutionary Guard Corps, may intensify its activities as the election approaches. Despite the probing not having escalated to actual hacking attempts, there is concern that foreign interference could amplify public unease regarding the voting process. U.S. officials emphasize that the integrity of the election is protected by various security measures. Concerns heightened after U.S. intelligence agencies accused Russian operatives of distributing disinformation through social media channels which targeted Democratic candidate Tim Walz. The surveillance of social media platforms has revealed a trend where both Russia and Iran may resort to misinformation to incite unrest during the lead-up to and post-election periods. Microsoft’s report indicates that while Iranian hackers have not yet engaged in a direct influence campaign for the upcoming election, their history of involvement raises alarms for U.S. officials, particularly recalling their past efforts to intimidate voters by impersonating right-wing groups during the 2020 election. Similarly, a group backed by the IRGC previously hacked Trump campaign documents that were subsequently leaked to the media.
Hackers affiliated with Iran have been increasingly active in probing U.S. electoral infrastructure, which reflects broader tactics used by various foreign entities to interfere in American politics. The specific group mentioned in the Microsoft report, Cotton Sandstorm, is likely linked to Iran’s Islamic Revolutionary Guard Corps (IRGC). This group’s activities are part of an ongoing concern that foreign powers are attempting to manipulate public perception and instigate discord around U.S. elections. Previous Iranian hacking incidents have included unauthorized access to voter registration data and efforts to intimidate voters during the last presidential election. This context highlights the persistent threat posed by state-sponsored cyber actors amidst an evolving information warfare landscape.
In summary, the recent findings from Microsoft regarding Iranian hacking activities present a significant concern for the integrity of U.S. elections. As foreign entities like those from Iran and Russia seek to sow discord and manipulate public sentiment, the importance of maintaining stringent cybersecurity measures becomes even more paramount. U.S. officials continue to monitor these activities closely, affirming that, while the current probe does not pose a direct threat to the electoral process, vigilance remains essential to mitigate the potential for misinformation and fear among voters.
Original Source: www.cnn.com







